Resilience as a cyber-security goal will lead to a more sophisticated and robust understanding of vulnerabilities. But it requires a major mindset and organisational shift.
As a conceptual framework, resilience is well-suited to cybersecurity, and in many ways it is superior to traditional risk-based approaches. By reframing the conversation from one of prevention to resilience, organisations will gain a far more profound insight into their own systems, and therefore a more meaningful understanding of their cybersecurity posture.
For one thing, an operational resilience lens turns traditional cybersecurity success-measures on their head. Ensuring ‘availability’ and ‘up-time’ sound like pragmatic goals, but they could also be indicators of fragility: if nothing is ever turned off, you cannot understand the inter-dependencies and resilience levels within the system. The principle being the importance of understanding how failure is likely to occur and confidence in recovery. Uptime and availability can obscure resilience risk.
This changes the central question of cybersecurity from how do we prevent this risk, to how do we continue to operate in the presence of degradation.
A resilience mind-set also takes us deeper, prompting a consideration of, not just a credible-threat scenario, but also the point at which dependent components fail, whether people, process or technology related.
Such a process will actually be familiar to cyber professionals in a different context, because it is almost identical to traditional ‘threat modelling’: first understand why someone is motivated to cause harm; then identify the paths of least resistance. Adopting this mind-set of understanding how systems fail at an organisational level is a profound and positive change. It should address a widespread lack of understanding of the complex inter-dependencies of systems and how they relate to important business services.
Inevitably, such an approach will surface hidden challenges for organisations, such as a lack of standardised documentation, as well as gaps in the understanding of data flows and how systems interact. Without these elements, it’s not possible to build a meaningful picture of resilience.
Cross-disciplinary scenario-testing
How is it possible to achieve this level of understanding (and to do so without actually unplugging anything)?
The answer is to bring together a cross-disciplinary view of systems, business owners, IT support, lines of business, front or back office, third-parties – in essence, all the stakeholder groups within a business service’s ecosystem. These parties would identify the architecture of the service, those items that are inherent to its applications, their inter-dependencies and relative importance. And they would then be able to validate where controls exist, and whether they are sufficient.
This approach will be familiar to those who have adopted ‘agile’ organisational structures, and many lessons that can be learned from organisations that have gone down this path. For instance, those organisations with DevOp capabilities, which have brought together developers and operations and IT teams to work together as single teams to develop products and systems in the most reliable and performant and reliable way. This is in stark contrast to the traditional ‘throw over the fence’ approach between different departments, which is inherently fragmented and create fragility. Such internal constructions within organisations directly impeded an organisation’s ability to be resilient.
Lessons from 2020
The past year has provided a salutary example of the importance of a joined-up approach to cyber resilience. The sudden work-from-home environment that confronted financial and other organisations during 2020 presented a scenario where new systems and processes were required to accommodate new ways of working, almost overnight.
Until recent years, a firm’s physical location was considered its safety perimeter. Inside the offices of major financial organisations, you would find clean-desk policies, auto-system time-outs, lock-screens. Everyone in the building protected by firewalls and software. Overnight, this perimeter was widened to the home of every employee and elevates us to different approaches to managing cyber security, such as those proposed by Zero Trust security strategies.
This raised some important practical questions around how organisations can get better at co-ordinating and collaborating cross-departmentally, and how they can ensure important business services are not overly-reliant on constrained or organisationally remote functions. Rather, they are empowered to operate independently with security built-in.
Security teams are normally chronically under-resourced and are therefore a bottle-neck in a centralised environment. To ensure resilience, business services must therefore be more federated, ensuring that business functions are adequately equipped and skilled to operate securely within defined boundaries. This is often enabled by providing self-service security capability that can be consumed by the wider business. Technologies that help to identify risks and that automate security controls (i.e. if an event happens, can it be automatically isolated without manual intervention) are also an important enabler of resilience.
The right question
Good governance and reporting are the bedrock of resilience, and this is no less the case in cybersecurity. Too often, board-level conversations begin with emphatic questions such as ‘are we secure?’ In a complex and uncertain operating environment, such questions can only be answered with extensive caveats. With a strategic pivot towards resilience, the question becomes ‘how much can we tolerate?’ This shift may appear subtle, but it represents a fundamental step-change in how security and resilience are considered and increases the sophistication to how the topic is discussed by business leadership. The level of knowledge required to keep something ‘on’ is very different to the knowledge required to understand how services continue to function in the absence of failure and loss events, such as data breaches. This evolution of security represents an exciting challenge for cybersecurity teams, and correctly implemented will have a radical effect on the real-world resilience of financial organisations.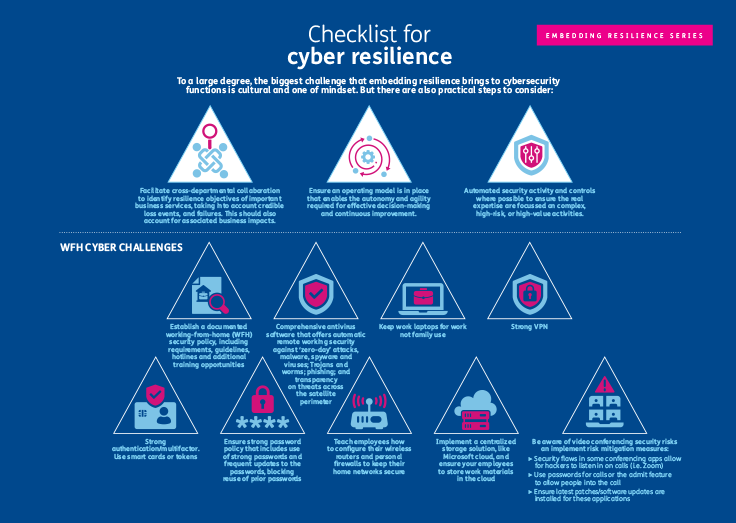 (click to enlarge image)
(click to enlarge image)
Visit our Re-frame Resilience content hub for more operational resilience insights.
If you would like to discuss this topic, or broader operational risk and resilience in more detail, or for more information on how to participate in our round-table series, please contact us.
Related Insights

Operational Resilience
It is critical to re-frame resilience to respond to client demands, evolving regulatory expectations, market forces, and global crises.
Read more
Corporate Governance and Internal Controls: the backbone of all businesses
The UK government has set out to overhaul audit and corporate governance to help restore trust in big businesses. Learn more.
Read more
The journey towards operational resilience maturity
The UK regulators’ operational resilience rules and guidance has come into force. Follow our guide to ensure a mature operational resilience framework.
Read more
Baringa Operational Risk Survey and Report 2020-2021 - Resilience put to the test
An annual survey of operational risk professionals provides an industry-led insight into FS best-practices and ongoing challenges. Read the operational risk review.
Read more